A couple of weeks ago we talked about website restrictions and how to enforce them without using a proxy. Now it’s time to prevent users of an Active Directory Domain Services from using specific applications.
Surprisingly enough, it’s much easier to restrict software than websites. You just need to access the domain controller and follow these steps.
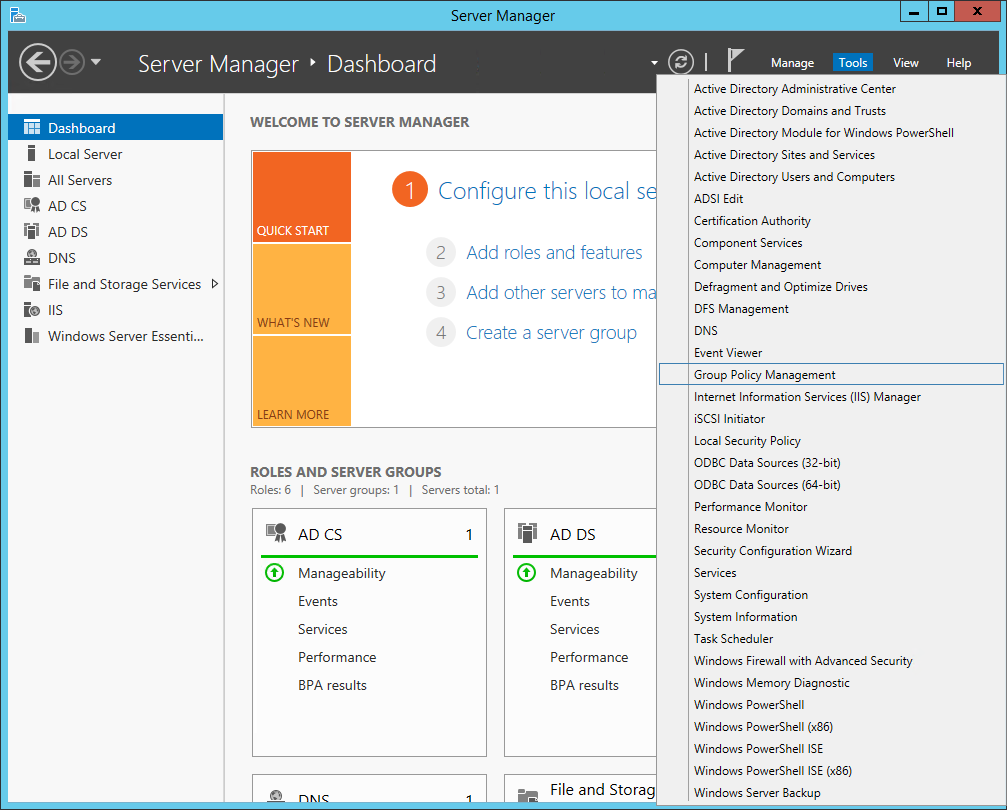
Open the Server Manager and launch the Group Policy Management:
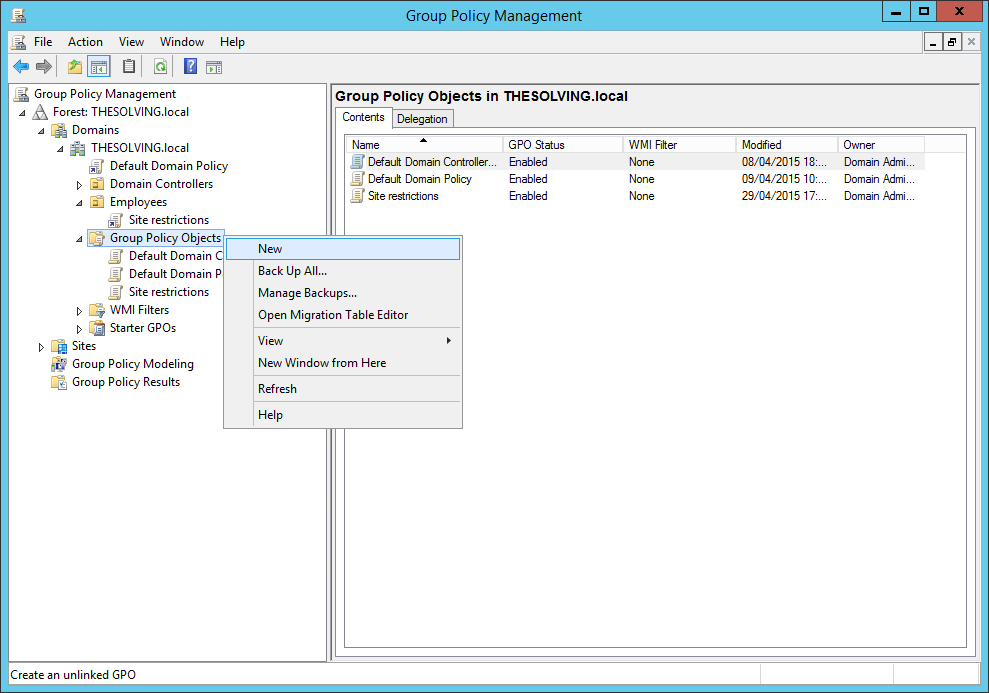
Create a new Group Policy Object:
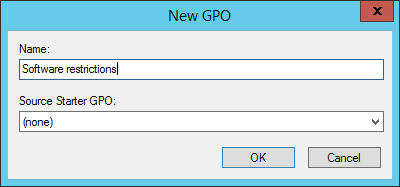
Give a name to the new GPO:
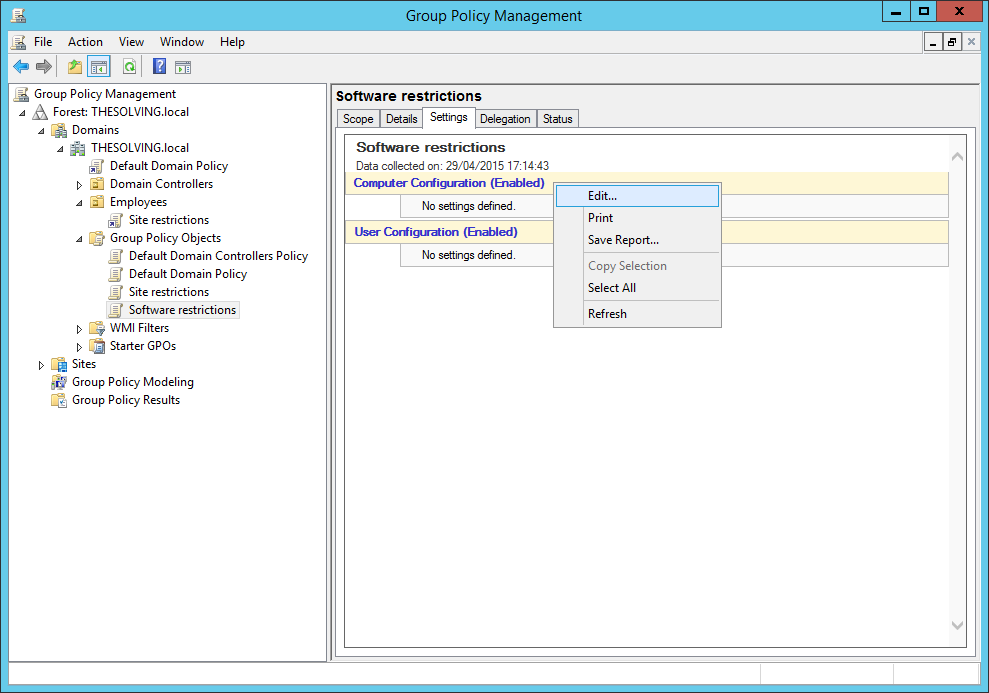
Edit the Computer Configuration:
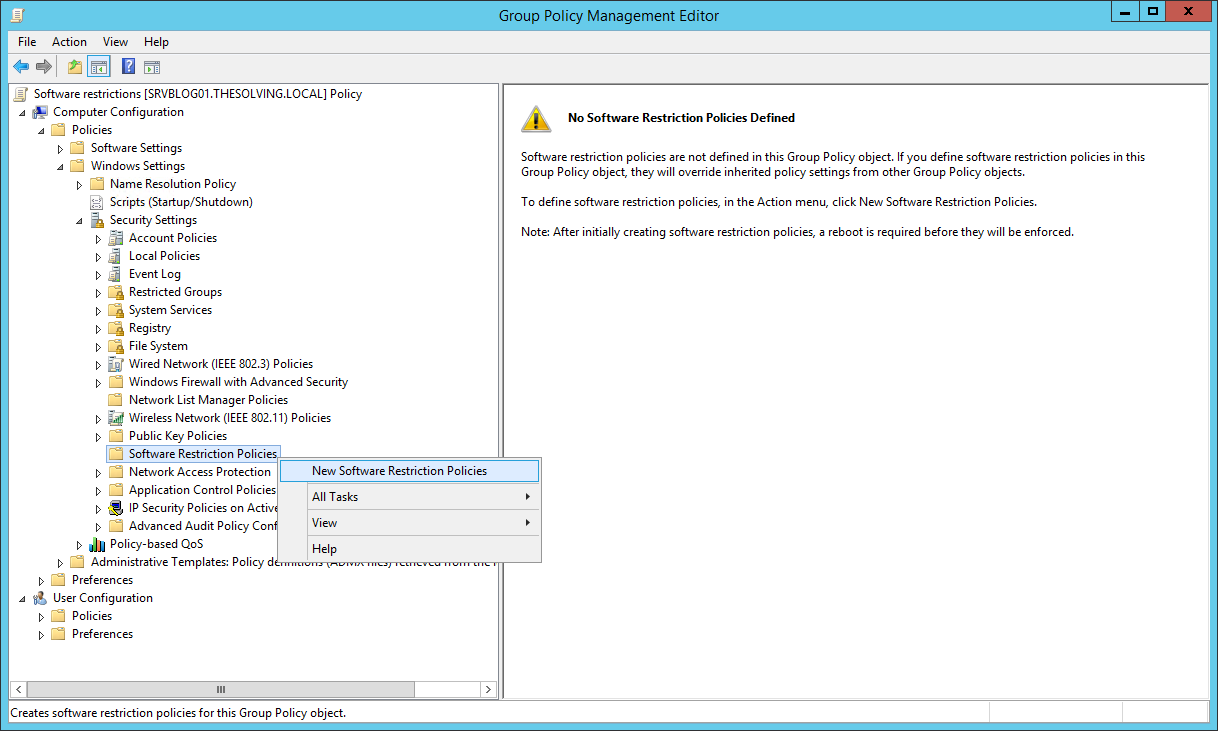
You will find the Software Restriction Policies under the path Computer Configuration –> Windows Settings –> Security Settings. Create New Software Restriction Policies:
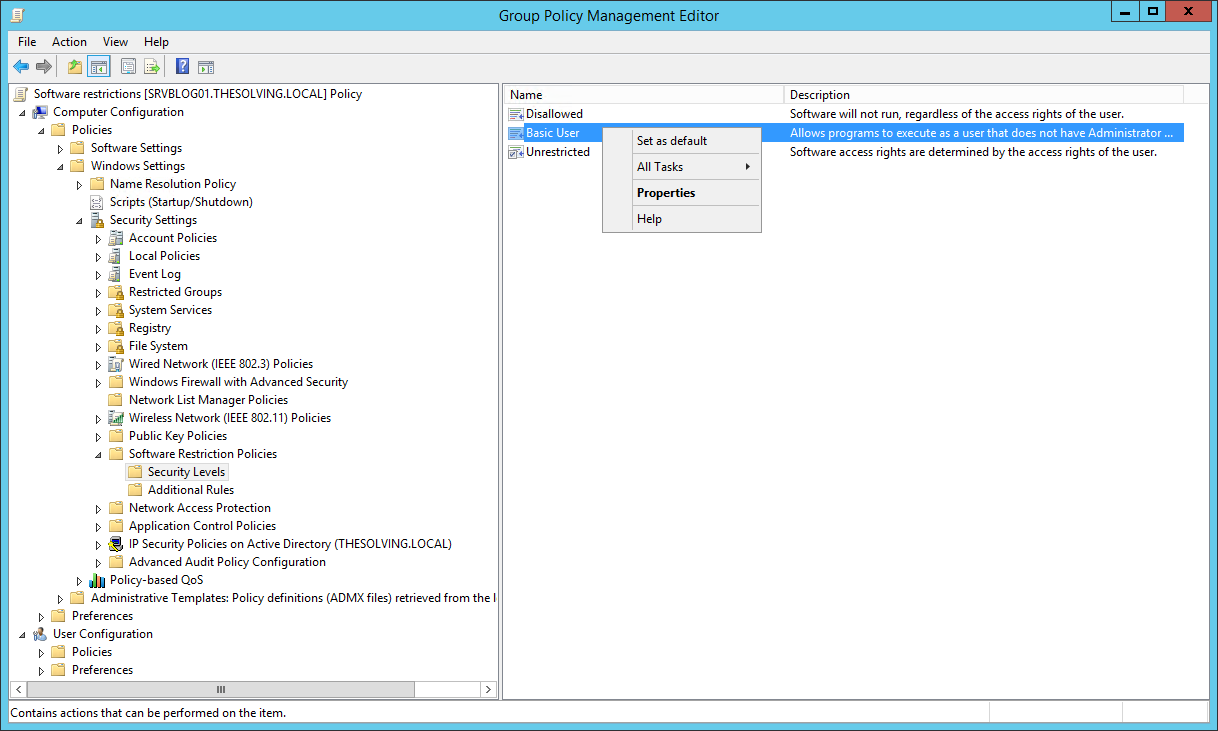
Under the Security Levels you will be able to configure the default software execution permissions for the desired group. Unrestricted (the default setting) doesn’t restrict software execution while Basic User allows only the execution of applications that don’t need Administrator rights. Disallowed forbids software execution. With a right-click you can set a new default configuration:
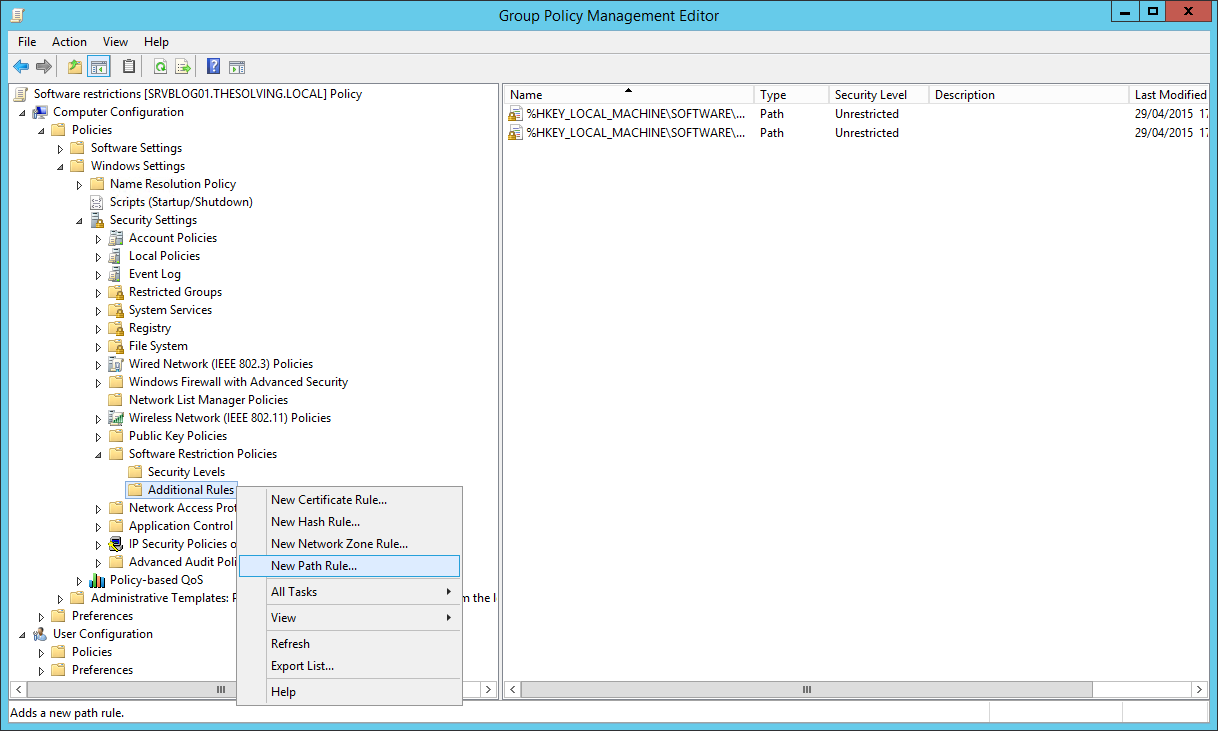
The Additional Rules are really important to restrict application usage. These rules override the default settings, so you can restrict all the applications and create specific rules to allow the execution of some of them or you can allow the execution of all the applications as default settings and restrict the few ones that bother you. We suggest to use the Path Rule, to restrict or allow the execution of files with a specific path:
In this example we are going to allow unrestricted execution for Mozilla Firefox. We can use the %UserProfile% parameter to create dynamic paths and restrict applications installed in the user folders:
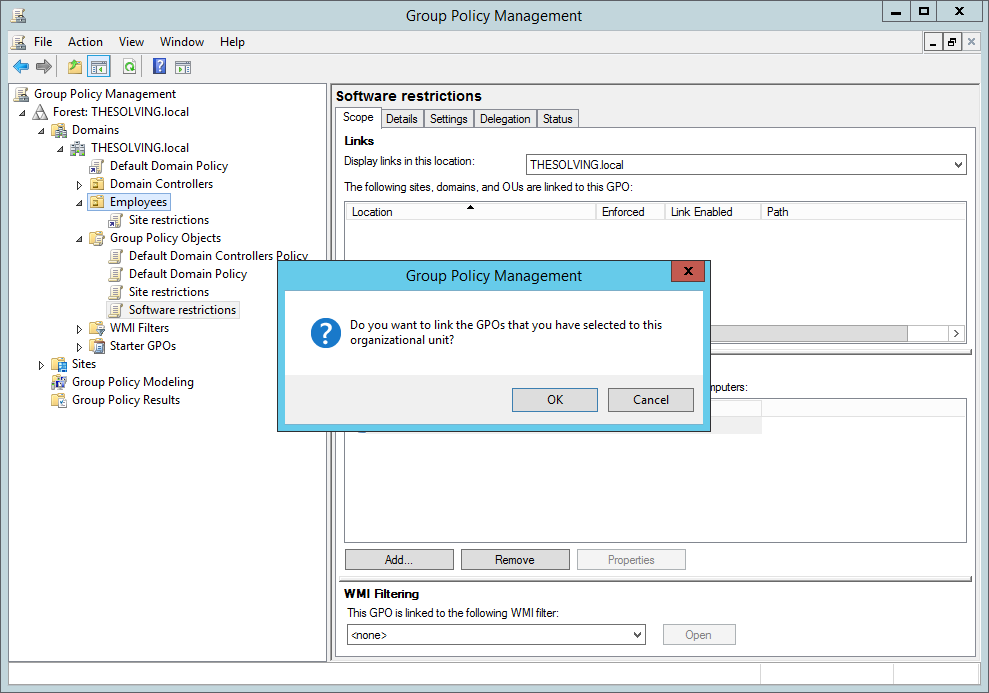
Your policy is ready. Now drag and drop it in the distribution group:
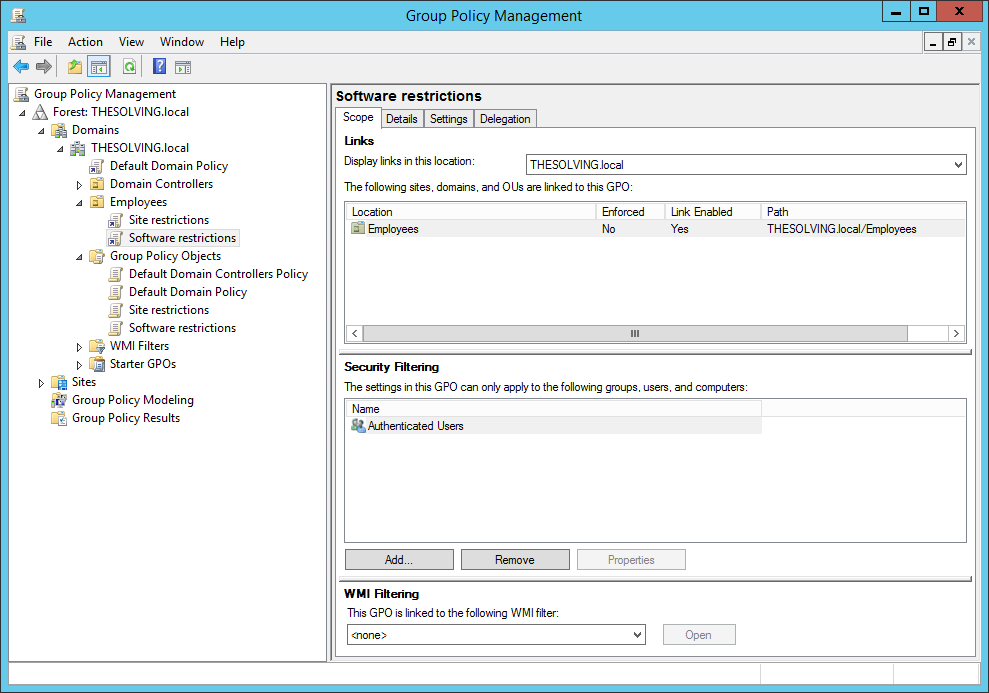
The policy will be now enforced:
Read related articles
How to use Sysprep in 2026: guide for sysadmins and MSPs
Sysprep in 2026: practical guide for sysadmins and MSPs Sysprep (System Preparation Tool) is the Microsoft tool used to prepare
A Guide to PowerShell – part 3
Welcome to part 3 of 3 of The Solving A guide to PowerShell. Check also Part 1 and Part 2.
A Guide to PowerShell – part 2
Welcome to part 2 of 3 of The Solving A guide to PowerShell. Click here for Part 1 and Part

 Italiano
Italiano
 Español
Español